Earlier this month I visited a colleague’s office. When I arrived, she offered me the password for WiFi like any gracious host would. Unfortunately, as soon as I hopped on the WiFi I noticed that I was on her company’s internal network. When I looked in “Network Neighborhood” I was able to see computers, printers, a server and more! Yikes!!!
Why is allowing guests on your company WiFi a bad idea? First off, depending on your industry, this may be against governance policies (or laws) like HIPAA or PCI compliance. Secondly, you don’t want to risk anyone bringing an infected computer into your environment. Even if every computer in your network is protected, there’s no reason to risk allowing “dirty” computer inside that could wreak havoc on your systems.
Luckily it’s easy to secure your company’s information assets AND provide secure guest WiFi at the same time. Here’s how to do it.
1. Pick the Strongest WiFi Encryption
Step one to securing your wireless network is easy. Just make sure you have selected WPA2 with AES for your wireless encryption type. If your wireless system has options for both “WPA2 Personal” and “WPA2 Enterprise” pick WPA2 Personal. WPA2 Enterprise requires extra authentication servers that your company might not have. If you have to choose between AES and TKIP, AES is the more secure option. For more detail on exactly what makes WPA2 with AES more secure than other wifi security combinations feel free to read on here but for now just remember:
Accept nothing less than WPA2 with AES encryption. WEP, WPA, and WPA-mixed are not secure.
If your wireless security doesn’t offer WPA2 with AES, try upgrading the firmware of your wireless equipment. If after a firmware upgrade WPA2 still isn’t available then it’s probably time to upgrade your wireless hardware. Either that or you should just consider your wireless network an insecure outside network, which is ok for guest Internet access. You’d just have to have your employees VPN in.
If you do want to upgrade to a modern wireless network, you can get really great wireless coverage with really great security for really cheap these days. Any commercial-grade wireless networking hardware on the market today supports the WPA2/AES standards, including Ruckus, Meraki, and Cisco (all brands we like). Meraki wireless is probably the easiest to set up but Ruckus wireless is probably going to give you the best bang for your buck as far as performance and coverage, depending on the application.
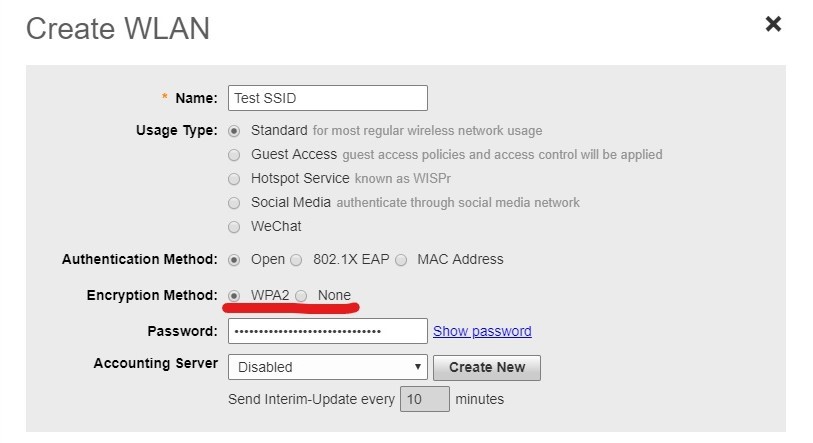
Here you can see that Ruckus Unleashed only offers two options for encryption – either WPA2 or nothing. I like it!
2. Pick a new Wireless Password
After you’ve made sure your wireless network uses strong encryption, the next step is to choose a strong “pre-shared key” for each of your wireless networks (see point 5 below). WPA2 supports pre-shared keys (PSKs) of up to 64 characters so use that length to get creative and create a LONG key! The longer a pre-shared key is, the harder it is to break. In fact, once a key gets to around 12 characters or so, it’s almost impossible for most people to crack. That said, computing power is getting cheaper every day so I err on the side of caution and use really long keys and passphrases for all my security applications. You can never be too careful!
Long is strong!
What’s a “passphrase” you ask? Excellent question! A passphrase is simply a few words strung together in order to make one long password or security key. Humans have a really hard time remembering short, nonsensical passwords with lots of different characters (example: 0af3dvsj) but we can remember a short simple phrase pretty easily. When we use a phrase like this to in place of a password we call it a passphrase.
For example, if I wanted to create a security key referencing my alma mater, I might use “GoPack!”. Unfortunately this key is short. Even with its moderate complexity (Upper-case letters, lower-case letters, and special characters all represented), it is really easy to crack. Even if I added a couple more characters to the end of the key, it could still be broken in under a week.
In contrast, consider “UNClikestocheat.” It has the same character classes as “GoPack!!!” but it’s almost twice as long. Because of its length, it’s much harder to crack. Best of all, it’s easy to remember (and not just because it’s true)!
GoPack!@# = Less than 1 week to crack
UNClikestocheat. = 800 million years to crack
Remember, “long is strong!” My test password above would take 800 million years to crack but it’s only 16 characters long. If you’re really concerned about security you can create a much longer passphrase for our own organization.
3. Hide the SSID of your Wireless Network
A well-trained hacker will be able to see your wireless network whether you hide it or not. That said, hiding your wireless network may deter passive interlopers. In order to hide your wireless network, go into your wireless settings and look for the phrase “Broadcast SSID” or “Hide SSID.” SSID stands for “Service Set Identifier” which is just a fancy way of saying “network name.” In plain english, hiding your SSID means your wireless network will no longer show up in the list of “available networks” on nearby wireless devices.
Once you find the SSID settings, make sure Broadcast is set to “OFF” or Hide is set to “On” for your internal networks. Don’t worry, though – your network is still there but after you disable the SSID broadcast it won’t appear to wireless clients any more. In order to connect to your hidden network, users will have to know the name of the network they want to connect to. If your organization uses Active Directory you can push wireless profiles out to your computer fleet using Group Policy in order to simplify wireless key changes.
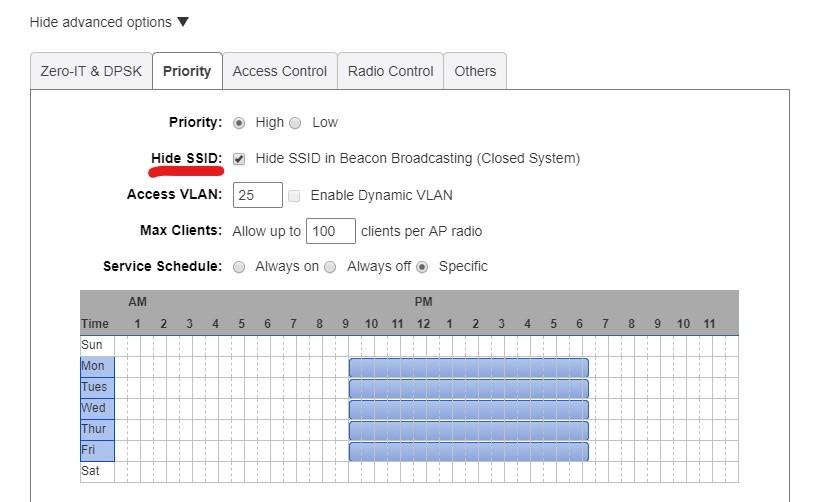
Within Ruckus Unleashed, the SSID can by hidden by ticking the “Hide SSID” box within the Advanced Options.
4. Turn your Wireless off When You’re Not Using It
Not every wireless solution has this feature but some vendors like Ruckus actually let you schedule times for your wireless networks to be on and off. For example, I usually get to the office late and leave late so my wireless network is only active from 9AM to 6:15PM, Monday through Friday (as demonstrated in the screenshot above). Granted, my wireless network is secured by a really long security key (see Step 2 above!) so I’m not too worried about someone breaking into my network BUT why even leave the wireless on if it’s not in use?
5. Separate your Wireless Networks
I saved this for last because it’s the hardest fix to put in place… but it’s also the most important. You should never (EVER!) allow guests to access your internal network. By giving guests your corporate wireless credentials, you are opening your environment up to unnecessary risk. Even if you trust the people to whom you’re providing Guest Internet access, you just have no way of knowing if their computers are infected with malware or not. You should consider all computers that are not under your (IT department’s) direct control as untrusted devices.
The way to keep untrusted devices away from your corporate IT assets is to contain them in their own wireless network. Just remember – in order to contain your Guest network and keep outside devices away from your corporate network, you have to do more than create a new wireless network (SSID). You actually have to create a whole new IP subnet on your firewall/router and a new VLAN to carry that subnet through your switches out to the wireless access points. Here’s a graphical representation of what I’m talking about:
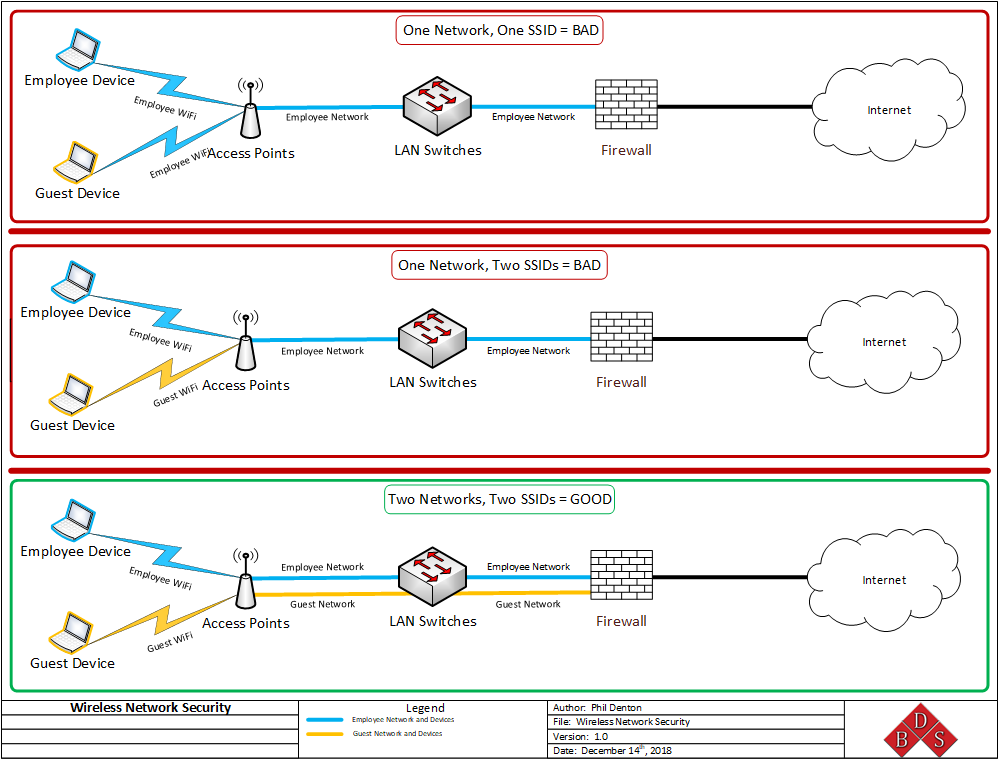
The third example is best because Guest and Employee wireless traffic is kept separate all the way to your firewall. By setting your networks up this way, you can create different firewall rules up for each class of wireless device. For example, you can allow Employee wireless devices to reach your servers but you can block guest access. Similarly, you can block employees from using social media at work but you can provide unfiltered Internet access to guests.
Securing your wireless network may seem challenging but if you can implement these five fixes you’ll be a lot more secure as a result. Please reference the graphic above as much as possible and if you need help locking down your WiFi feel free to say hello any time, or just contact us through Facebook or LinkedIn. Thanks for reading and until next time, stay safe, stay secure, and stay productive!




Leave A Comment